Mailbox Auditing in Exchange Online is one of the most critical security and compliance features available in Microsoft 365. In this guide, I will teach you Mailbox Auditing from an expert perspective—explaining how it works, why it matters, and how to configure and use it effectively in real enterprise environments.
By the end of this article, you’ll understand every important aspect of auditing, including default audit actions, investigation techniques, reporting, log retention, and how to use PowerShell to extract valuable insights. My goal is to train you through this blog as if we were performing hands‑on Exchange Online operations together.
So let’s begin your journey into mastering Mailbox Auditing in Exchange Online.
Table of Contents
1. What Is Mailbox Auditing in Exchange Online?
Mailbox auditing allows administrators and security teams to track who accessed a mailbox, what actions were taken, and when those actions occurred. Because cloud mailboxes are accessed from multiple devices and locations, Exchange Online builds auditing deeply into the service.
Auditing helps answer vital questions like:
- Who accessed a user’s mailbox?
- User copy message to another folder
- Were any messages deleted or moved?
- Did an administrator log in to a mailbox?
- Did a delegate send email on behalf of a user?
- Was sensitive content exported or forwarded?
- Modify permission from folder
- Add/ remove deligate mailbox permission
- Update inbox rule from outlook client
These capabilities make Mailbox Auditing in Exchange Online essential for:
- Security investigations
- Insider threat detection
- Compliance and legal inquiries
- Forensics
- Monitoring privileged activities
2. Mailbox Auditing Enabled by Default
In Exchange Online, mailbox auditing is enabled by default for all mailboxes. This includes:
- User mailboxes
- Shared mailboxes
- Resource mailboxes
This default‑on behavior reduces configuration overhead and ensures complete visibility across your tenant.
You can verify auditing status with PowerShell:
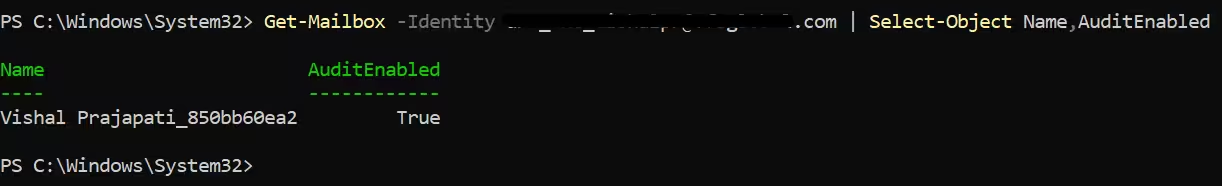
Get-Mailbox -Identity user@domain.com | Select-Object Name,AuditEnabledIf you ever find it disabled (rare), re-enable it:
Set-Mailbox -Identity user@domain.com -AuditEnabled $true3. Audit Log Types in Exchange Online
Mailbox auditing captures three categories of actions:
3.1 Owner Actions
Actions taken by the mailbox owner themselves.
Examples:
- Message deletion
- Message movement
- Message creation
- Folder creation/ deletion
- Sending mail
3.2 Delegate Actions
Actions taken by someone who has permissions on the mailbox.
Examples:
- Send As
- Send on Behalf
- Reading messages
- Moving items
3.3 Admin Actions
Actions performed by administrators.
Examples:
- Mailbox login
- Search performed on behalf of user
- Permission updates
Mailbox auditing tracks all of these by default.
4. Default Audit Actions Captured
Microsoft maintains a built-in set of mailbox auditing actions.
You can view them with:
Get-Mailbox -Identity user@domain.com | Select -ExpandProperty AuditOwnerTypical actions include:
Owner actions:
- Update
- MoveToDeletedItems
- SoftDelete
- HardDelete
- UpdateFolderPermissions
- UpdateInboxRules
- UpdateCalendarDelegation
- ApplyRecord
- MailItemsAccessed
- Send
Delegate actions:
You can view them with:
Get-Mailbox -Identity dxc_exc_vishalpr@vfsglobal.com | Select -ExpandProperty AuditDelegate- Update
- MoveToDeletedItems
- SoftDelete
- HardDelete
- SendAs
- SendOnBehalf
- Create
- UpdateFolderPermissions
- UpdateInboxRules
- ApplyRecord
- MailItemsAccessed
Admin actions:
You can view them with:
Get-Mailbox -Identity dxc_exc_vishalpr@vfsglobal.com | Select -ExpandProperty Auditadmin- Update
- MoveToDeletedItems
- SoftDelete
- HardDelete
- SendAs
- SendOnBehalf
- Create
- UpdateFolderPermissions
- UpdateInboxRules
- UpdateCalendarDelegation
- ApplyRecord
- MailItemsAccessed
- Send
These auditing categories allow full visibility of mailbox behavior.
5. Why Mailbox Auditing Matters
5.1 Security and Threat Detection
Mailbox auditing helps identify suspicious activities like:
- Unexpected logins
- Unauthorized deletions
- Delegate misuse
- Admin abuse
5.2 Regulatory Compliance
Industries like finance, healthcare, and government require mailbox access logging.
5.3 Forensics and Investigations
During security incidents, mailbox audit logs reveal the timeline of events.
5.4 Accountability
Audit logs provide clear evidence of who did what.
For an Exchange Online administrator, mastering Mailbox Auditing in Exchange Online is mandatory for secure operations.
How to Become a Microsoft 365 Support Engineer: Step-by-Step Career Guide
6. Configuring Custom Mailbox Auditing Policies
Microsoft introduced the unified audit policy, which applies default audit actions across all mailboxes. But you can also customize auditing if needed.
To adjust owner actions:
Set-Mailbox -Identity user@domain.com -AuditOwner @{Add="Update"; Remove="Move"}To adjust delegate actions:
Set-Mailbox -Identity user@domain.com -AuditDelegate @{Add="SendAs"}To adjust admin actions:
Set-Mailbox -Identity user@domain.com -AuditAdmin @{Add="MailboxLogin"}Use customization only if necessary—default settings are sufficient for most organizations.
7. Accessing Mailbox Audit Logs
Mailbox audit logs are accessed through Microsoft Purview > Audit or through PowerShell.
7.1 Using the Purview Audit Portal
Go to:
Microsoft 365 Admin Center → Microsoft Purview→ Solutions→ Audit
Search using criteria under exchange mailbox activities:
- Select user
- Date/time
- Mailbox Activities
- Record Types
Audit entries include key details:
- UserId
- Operation
- FolderPath
- ClientIPAddress
- LoginType
- LogonUserDisplayName
8. Using PowerShell for Mailbox Auditing (Most Powerful Method)
PowerShell gives the most control for deep investigation.
8.1 Search for mailbox audit log entries
Search-UnifiedAuditLog -StartDate (Get-Date).AddDays(-7) -EndDate (Get-Date) -Operations MailItemsAccessed -UserIds user@domain.com8.2 Export logs to CSV
Search-UnifiedAuditLog -StartDate 3/1/2026 -EndDate 3/4/2026 -UserIds user@domain.com | Export-Csv C:\reports\mailboxaudit.csv -NoTypeInformation8.3 Check who accessed a mailbox
Search-UnifiedAuditLog -StartDate (Get-Date).AddDays(-30) -EndDate (Get-Date) -FreeText "SendAs"These commands allow deep inspection of activity.
9. Key Audit Actions Explained
Let’s break down some of the most important actions tracked by Mailbox Auditing in Exchange Online.
SendAs
Someone sent email pretending to be that user.
SendOnBehalf
Delegate sent mail on behalf of the user—visible to recipient.
MailboxLogin
Admin logged into the mailbox (usually a red flag).
HardDelete
Message deleted permanently (bypassing Recoverable Items folder).
SoftDelete
Message moved to Deleted Items or Recoverable Items.
MailItemsAccessed
Tracks message reads and previews—enabled by Microsoft for insider threat detection.
10. Retention of Mailbox Audit Logs
Audit log retention depends on the license:
Microsoft 365 E3
- 180 days retention
Microsoft 365 E5 / Purview Audit (Premium)
- 365 days to 10 years
- Complete forensic-level detail
If your organization requires long-term audit retention, E5 is strongly recommended.
11. Investigating Suspicious Activity
Here’s how to perform a real-world investigation.
11.1 Scenario: A user reports “someone read my emails”
Search for delegate access:
Search-UnifiedAuditLog -StartDate (Get-Date).AddDays(-14) -EndDate (Get-Date) -Operations MailItemsAccessed -UserIds user@domain.comCheck IP address, login type, and accessed items.
11.2 Scenario: Messages disappearing from a mailbox
Search for hard and soft deletes:
Search-UnifiedAuditLog -Operations HardDelete,SoftDelete -UserIds user@domain.com11.3 Scenario: Unauthorized admin login
Search for admin mailbox login actions:
Search-UnifiedAuditLog -Operations MailboxLogin | ? {$_.LogonType -eq "Admin"}12. Reporting and Automation
Create an automated audit report for all VIP mailboxes:
$VIPs = Get-Mailbox -Filter {CustomAttribute1 -eq "VIP"}
foreach ($user in $VIPs) {
Search-UnifiedAuditLog -StartDate (Get-Date).AddDays(-1) -EndDate (Get-Date) -UserIds $user.UserPrincipalName |
Export-Csv "C:\AuditReports$($user.Alias)_daily.csv" -NoTypeInformation
}You can schedule this script to run daily or weekly.
13. Best Practices for Mailbox Auditing in Exchange Online
Always leave mailbox auditing enabled
This ensures full coverage.
Use Purview Audit Premium for long-term retention
Especially for regulated industries.
Review high-risk actions (SendAs, HardDelete, MailboxLogin)
These are most associated with abuse.
Monitor VIP mailboxes
Executives are prime targets for phishing and insider threats.
Automate reports
Saves time and standardizes investigations.
14. Common Issues and How to Solve Them
Issue: “No audit data found”
Fix: Expand date range or confirm mailbox activity.
Issue: Audit logs incomplete
Fix: Verify that the mailbox is syncing to the unified audit log.
Issue: Delegate actions not visible
Fix: Ensure mailbox permissions are configured correctly.
15. Final Thoughts
By following this guide on Mailbox Auditing in Exchange Online, you’ve gained expert-level understanding of how auditing works, how to configure it, and how to perform deep forensic investigations in real-world environments.
Mailbox auditing is far more than a compliance feature—it’s an essential security pillar that provides visibility, accountability, and protection for your organization’s most sensitive data.